Traditional paper passport is gradually being replaced by its digital counterpart. While this shift promises greater convenience and efficiency for travelers, it also raises important questions about the security implications of entrusting sensitive personal information to digital platforms. Reports suggest this transition to digital passports is gaining momentum, with several countries already implementing or actively developing digital travel document systems.
This article delves into the security landscape of digital passports, exploring the measures in place to protect against potential risks and the challenges that lie ahead.
What is a Digital Passport?
A digital passport is an electronic version of a traditional passport. Instead of carrying a physical booklet, your passport information is securely stored on a mobile device or an online platform. It contains the same essential details, such as your name, nationality, and travel history, but in a more efficient and modern format.
Digital passports often incorporate biometric technology, such as facial recognition, fingerprints, or iris scans, to verify the identity of the passport holder. This integration of biometrics adds an extra layer of security, making it more difficult for unauthorized individuals to use a stolen or forged passport.
Benefits of Digital Passports
The adoption of digital passports offers several advantages for both travelers and governments:
- Increased Efficiency and Convenience: Digital passports can expedite the process at security checkpoints, reducing wait times and making travel more efficient. Travelers can breeze through airports with greater ease, enjoying a smoother and faster travel experience.
- Enhanced Security: Digital passports are more difficult to forge or steal than traditional passports. The use of encryption, digital signatures, and biometric technology makes it significantly harder for criminals to tamper with or replicate these documents.
- Improved Identity Verification: Biometric technology and digital signatures make it more difficult for unauthorized individuals to use a stolen or forged passport. This enhances the accuracy and reliability of identity verification at border crossings.
- Reduced Contact Points: Digital IDs can reduce contact points for passengers, minimizing the spread of germs and diseases. This is particularly relevant in today's health-conscious world.
- Easier Updates: Renewing or updating passport information can be done online, eliminating the need to wait for a new physical document. This streamlines the process and saves travelers valuable time.
- Environmentally Friendly: Digital passports reduce the need for paper-based travel documentation. This contributes to a more sustainable approach to travel.
Benefits for Governments and Authorities
Beyond the benefits for travelers, digital passports offer significant advantages for governments and authorities:
- Enhanced Border Security: Digital passports provide a more secure and reliable way to verify the identity of travelers, strengthening border security and reducing the risk of fraudulent entries.
- Improved Efficiency: The use of digital passports can streamline border control processes, reducing wait times and improving the efficiency of immigration procedures.
- Cost Reduction: By reducing the need for manual processing and physical document handling, digital passports can lead to cost savings for governments.
- Quicker Crisis Response: In emergency situations, digital passports can facilitate quicker identification and communication with citizens, enabling more efficient crisis response and support.
Security Measures in Digital Passports
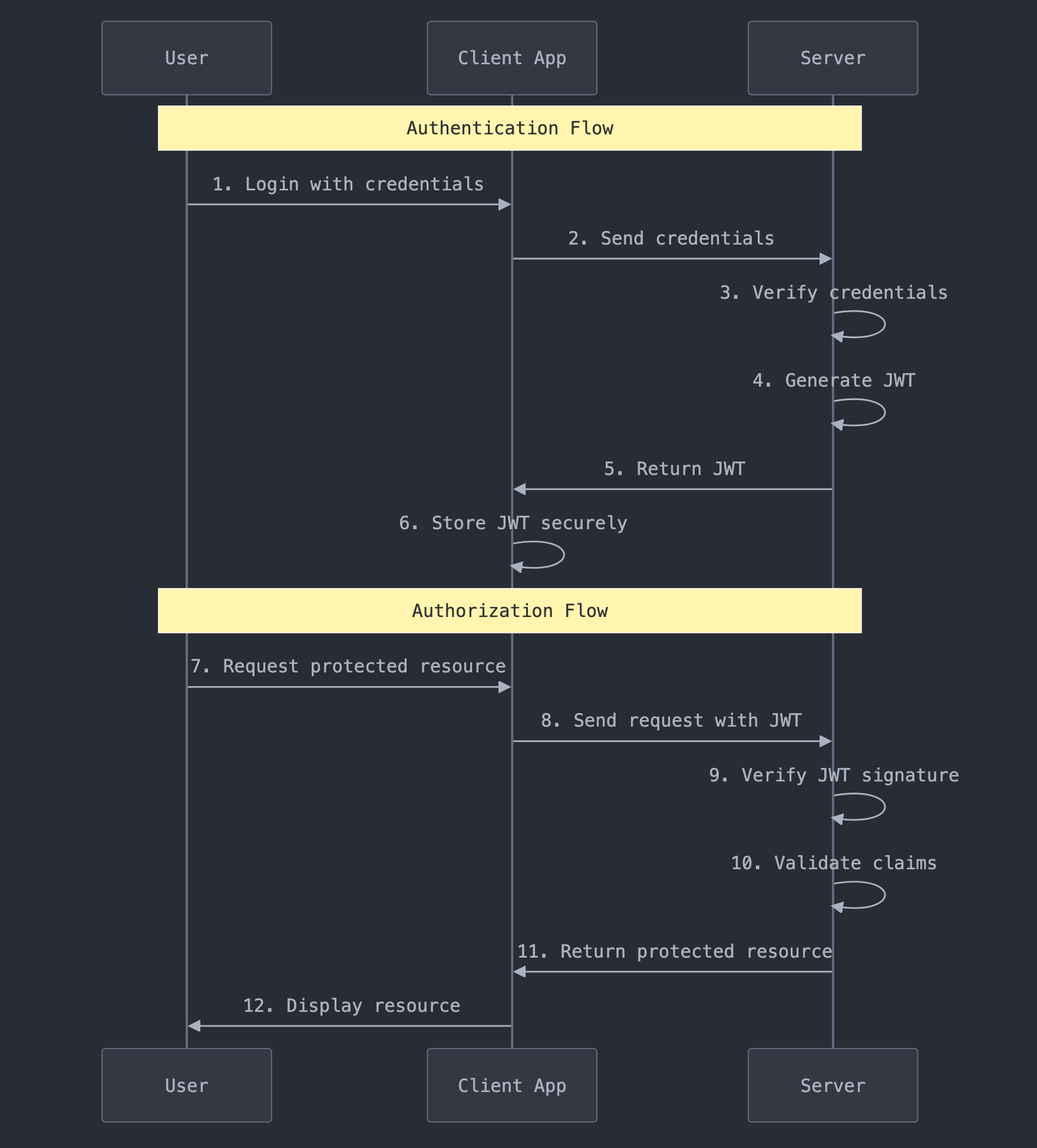
Digital passports employ a multi-layered approach to security, incorporating various measures to protect against potential threats:
- Biometric Verification: As mentioned earlier, digital passports are often linked to biometric data, such as facial recognition, fingerprints, or iris scans, to ensure that the person presenting the passport is the legitimate owner.
- Encryption: Passport data is encrypted to protect it from unauthorized access. This ensures that even if a device is lost or stolen, the data remains secure.
- Secure Digital Scans: Digital passports can be scanned at checkpoints using QR codes, NFC (near-field communication), or other secure methods to verify identity. These methods provide a quick and reliable way to authenticate the passport.
- DTC Triad: The security architecture for Digital Travel Credentials (DTCs) is based on a "security triad" consisting of mobile, central, and border control components. The mobile component resides on the traveler's device, the central component is a secure cloud platform, and the border control component allows authorities to verify the traveler's identity. This triad ensures a secure and efficient process.
- Chip Security Mechanisms: Digital passports utilize various chip security mechanisms to protect the data stored on the chip. These include:
- Digital Signatures: Digital signatures are used to ensure the authenticity and integrity of the data stored on the passport chip.
- Public Key Infrastructure (PKI): PKI technology is used to prevent the alteration of data on the chip.
- Active Authentication (AA): This helps to prevent the cloning of biometric passports.
- Passive Authentication (PA): This detects chip modifications.
- Basic Access Control (BAC): This protects the communication channel between the passport chip and the reader.
- Extended Access Control (EAC): This provides extra protection for iris scans and fingerprint data.
- Protective Measures:
- Metallic Mesh: RF blocking material embedded in the passport booklet prevents unauthorized reading or "skimming" of data.
- Random UID (RUID) Feature: This issues a new random UID each time the chip is accessed, preventing tracking.
It is important to emphasize that security in digital passports requires a holistic approach. This involves not only implementing robust technological measures but also fostering user awareness, establishing strong data protection laws, and promoting international collaboration to ensure the integrity and security of digital travel document systems.
Potential Risks Associated with Digital Passports
While digital passports offer numerous benefits, it is crucial to acknowledge and address the potential risks:
- Data Breaches and Hacking: As with any digital system, there is always a risk of data breaches and hacking. If passport data is compromised, it could be used for identity theft or other malicious purposes. Governments and technology providers must prioritize robust security measures and invest in continuous monitoring and improvement to mitigate these risks.
- Loss or Theft of Device: If a device containing a digital passport is lost or stolen, the passport data could be accessed by unauthorized individuals. This highlights the importance of device security measures, such as strong passwords, biometric authentication, and remote data wiping capabilities.
- Technical Issues: Digital passports rely on technology, which can malfunction or be unavailable. This could cause problems for travelers who are unable to access their passport information when needed. Contingency plans and offline backups should be in place to address such situations.
- Privacy Concerns: There are concerns about the privacy implications of storing sensitive personal information on digital platforms and the potential for government surveillance. Clear regulations and safeguards are needed to ensure that digital passport systems prioritize data protection and individual privacy.
- Discrimination: The use of facial recognition technology in digital passports raises concerns about potential bias and discrimination against certain groups. Thorough testing and ongoing evaluation are essential to ensure fairness and prevent discriminatory outcomes.
- Unofficial Digital IDs and "Infostealers": Storing passport scans or other unofficial digital IDs on personal devices can pose significant security risks. These practices can make individuals vulnerable to "infostealers," a type of malware that targets sensitive information stored on devices. Infostealers can compromise personal data and lead to identity theft. It is crucial to avoid storing sensitive documents insecurely and to be cautious of potential phishing attempts or suspicious messages.
User Responsibility and Best Practices
While governments and technology providers have a responsibility to ensure the security of digital passport systems, users also play a crucial role in mitigating risks. Here are some best practices for travelers using digital passports:
- Protect Your Device: Use strong passwords, biometric authentication, and keep your device software updated to prevent unauthorized access.
- Be Mindful of Public Wi-Fi: Avoid using public Wi-Fi networks to access sensitive information, as these networks can be vulnerable to hacking.
- Manage Location Services: Be aware of how you are using location services and adjust privacy settings to avoid unintentional data exposure.
- Practice Social Media Savvy: Exercise caution when sharing travel updates on social media and avoid posting photos of your passport or other travel documents.
- Be Wary of Phishing Attempts: Be skeptical of unsolicited communications and verify the source before sharing any information.
Current State of Adoption
Several countries are leading the way in the adoption of digital passports and travel documents:
- Finland: Finland launched the world's first digital passport in 2023, allowing travelers on certain flights to use a mobile app instead of a physical passport. This pilot program is being closely monitored to assess its feasibility and user satisfaction.
- Ukraine: In 2024, Ukraine granted digital passports the same legal status as physical ones. This demonstrates a commitment to digital transformation and the recognition of digital documents as valid proof of identity.
- Singapore: Singapore introduced a digital health passport called HealthCerts in 2023 to store and present COVID-19 test results and vaccination records. This initiative facilitated safer travel during the pandemic and showcased the potential of digital health documents.
- Estonia: Estonia has a long-established digital ID system that allows citizens to access various services online, including travel-related ones. This system has been highly successful and serves as a model for other countries.
The TSA's Role in the US
In the United States, the Transportation Security Administration (TSA) is actively exploring the use of digital IDs and facial recognition technology to enhance security and streamline travel. The TSA emphasizes that participation in facial recognition programs is voluntary and that all data and images are protected and not used for law enforcement or surveillance purposes.
Countries Planning to Use Digital Travel Documents
Many countries are actively working towards implementing digital travel document systems. These include:
- The UK: The UK is expanding its Electronic Travel Authorization (ETA) system, which will eventually apply to all visitors and transit passengers who do not currently need a visa for short stays.
- The EU: The European Union is developing the European Travel Information and Authorization System (ETIAS), similar to the US ESTA and UK ETA, and is also working on a digital passport system.
- Thailand: Thailand is implementing an ETA system to increase tourism and spur economic growth.
- Israel: Israel is set to roll out its own ETA framework.
- South Africa: South Africa is actively preparing to implement an ETA system by 2029.
This widespread adoption of digital travel documents indicates a global shift towards more efficient and secure border control processes.
The Future of Digital Passports
The future of digital passports is likely to be characterized by:
- Wider Adoption: More countries are expected to adopt digital passport programs in the coming years. This will create a more interconnected and efficient global travel system.
- Global Standardization: International collaboration on standards and compatibility will be crucial to ensure the seamless use of digital passports across borders. Organizations like ICAO will play a key role in establishing these standards.
- Integration with Other Documents: Digital passports could be integrated with other travel documents, such as visas, vaccination records, and boarding passes, creating a single platform for all travel needs. This would further streamline the travel experience.
- Quantum-Resistant Security: As quantum computing advances, digital passports will need to incorporate quantum-resistant algorithms to protect against new threats. This will ensure the long-term security of digital travel documents.
- Increased Use of AI: Artificial intelligence will play a greater role in enhancing passport design, verification, and fraud detection. AI can help to improve the accuracy and efficiency of identity verification processes.
Expansion to Other Domains
The concept of digital identity is not limited to travel documents. The research also mentions the emergence of digital product passports. These digital passports provide detailed information about a product's origin, production process, and environmental impact. This technology has the potential to enhance supply chain security, combat counterfeiting, and increase consumer trust.
Conclusion
The transition to digital passports represents a significant step towards a more efficient and secure travel experience. While potential risks need to be addressed, the benefits of digital passports, such as increased convenience, enhanced security, and reduced environmental impact, are undeniable. As technology continues to evolve, digital passports will likely become the norm for international travel, paving the way for a more seamless and interconnected world.
This shift also has broader implications for global mobility, national security, and individual privacy. The increasing reliance on digital identity raises important questions about data protection, surveillance, and the balance between security and freedom. It is crucial to establish clear legal frameworks, robust security measures, and ethical guidelines to ensure that digital passport systems are used responsibly and protect individual rights.
Furthermore, the evolving nature of technology and the emergence of new threats, such as quantum computing and AI-generated fraud, necessitate ongoing evaluation and adaptation of security measures. Continuous research and development are essential to stay ahead of potential vulnerabilities and ensure the long-term integrity and security of digital passport systems.
https://bit.ly/3F7k94r
https://bit.ly/3XvPmVj
https://images.unsplash.com/photo-1594570322022-e7026b28a6c1?crop=entropy&cs=tinysrgb&fit=max&fm=jpg&ixid=M3wxMTc3M3wwfDF8c2VhcmNofDM0fHxwYXNzcG9ydCUyMFJJUHxlbnwwfHx8fDE3NDA1MTcxMzZ8MA&ixlib=rb-4.0.3&q=80&w=2000
https://guptadeepak.weebly.com/deepak-gupta/the-rise-of-digital-passports-navigating-the-security-implications