Startups often face a critical challenge: how to achieve significant growth with limited financial resources. This is where the concept of "bootstrapping growth" comes into play. By leveraging creativity, hustle, and strategic thinking, startups can build a solid foundation for growth without relying on substantial outside investment. This article delves deep into the strategies and tactics that can help B2B SaaS startups bootstrap their way to success.
Understanding Bootstrapped Growth
Bootstrapped growth refers to the process of growing a business using minimal financial resources, often relying on the founder's personal savings, revenue generated from early customers, and creative, low-cost growth strategies. For B2B SaaS startups, this approach offers several advantages:
- Maintains equity and control for founders
- Forces a focus on profitability and sustainable growth
- Encourages creativity and resourcefulness in problem-solving
- Builds a lean, efficient company culture from the start
However, bootstrapping also presents unique challenges, particularly in the highly competitive SaaS space where well-funded competitors can outspend you on marketing and development. To overcome these challenges, startups need to be strategic, resourceful, and laser-focused on activities that drive real value.
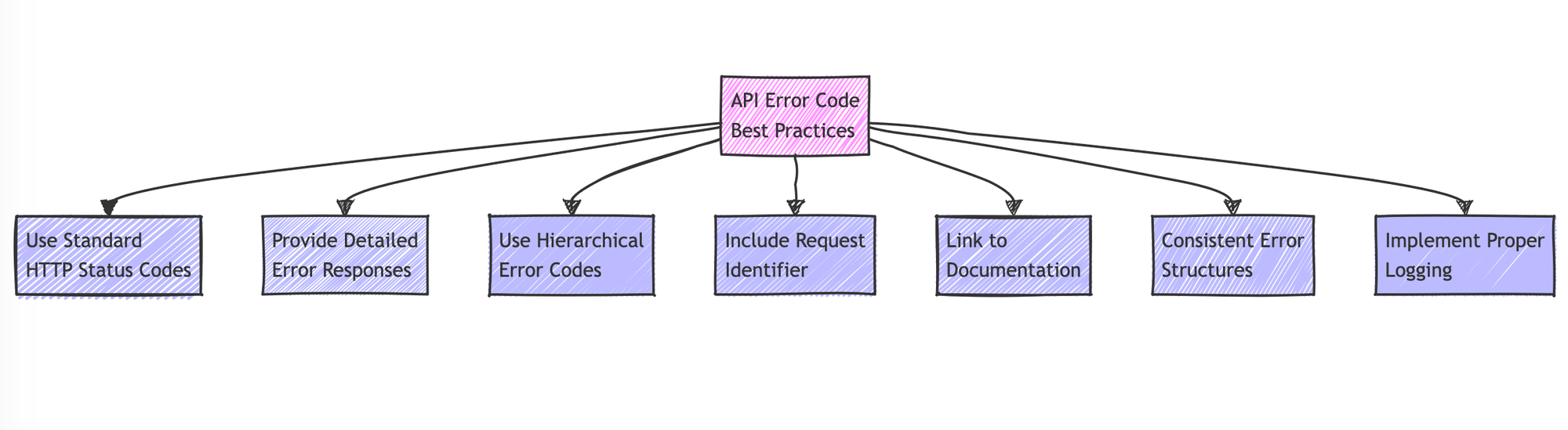
Key Strategies for Bootstrapping B2B SaaS Growth
1. Leverage Free and Low-Cost Marketing Tools
In the early stages, every dollar counts. Fortunately, there's a wealth of free and low-cost tools available that can help startups punch above their weight class:
- Content Marketing: Use tools like WordPress (free), Canva (freemium), and Unsplash (free) to create and distribute high-quality content.
- Email Marketing: Leverage platforms like Mailchimp (free up to 2,000 contacts) or Brevo (free up to 300 emails per day) for email campaigns.
- Social Media Management: Use Buffer (free plan available) or Adobe Express (limited free plan) to manage and schedule social media posts.
- SEO: Utilize free tools like Google Search Console, Google Analytics, and Ubersuggest for keyword research and site optimization.
- Customer Relationship Management (CRM): Start with HubSpot CRM (free) or Freshsales (free tier available) to manage customer relationships.
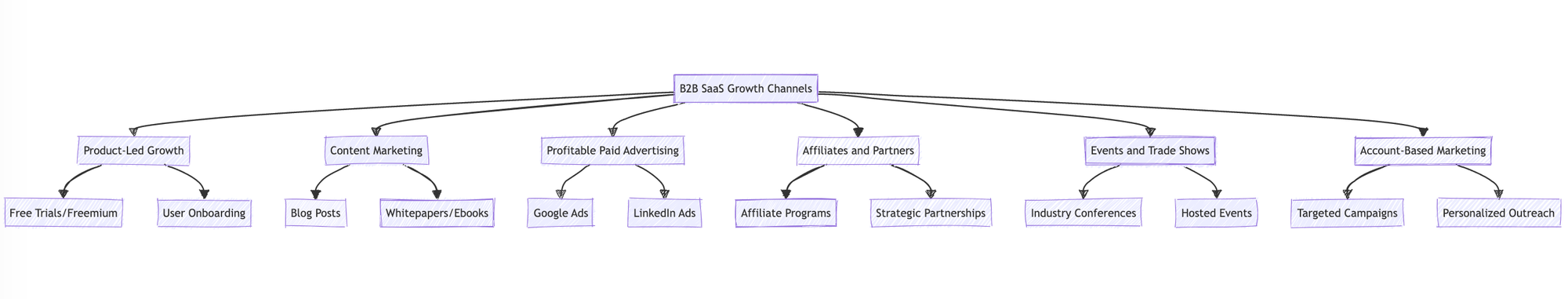
2. Focus on Organic Growth Channels
Paid advertising can quickly drain a startup's limited resources. Instead, focus on organic growth channels that require time and effort but minimal financial investment:
- Content Marketing: Create in-depth, valuable content that addresses your target audience's pain points. This could include blog posts, whitepapers, eBooks, and case studies.
- SEO: Optimize your website and content for search engines to drive organic traffic. Focus on long-tail keywords relevant to your niche.
- Social Media: Build a presence on platforms where your target audience is active. Share valuable content, engage in conversations, and build relationships.
- Community Building: Create or participate in online communities (e.g., Slack groups, LinkedIn groups, Reddit) where your target audience gathers.
- Open-Source Strategy: If applicable, consider open-sourcing part of your product to build credibility and attract developers.
3. Implement Growth Hacking Techniques
Growth hacking involves using creative, low-cost strategies to acquire and retain customers. Some effective techniques for B2B SaaS startups include:
- Product Hunt Launch: Orchestrate a well-planned launch on Product Hunt to gain initial traction and feedback.
- Referral Programs: Implement a referral system that incentivizes current users to bring in new customers.
- Strategic Partnerships: Partner with complementary businesses to cross-promote each other's products.
- Freemium Model: Offer a free tier of your product to attract users and upsell them to paid plans.
- Micro-Influencer Collaborations: Partner with niche influencers in your industry for product reviews or guest content.
4. Optimize for Customer Success and Retention
In B2B SaaS, retaining and expanding existing accounts is often more cost-effective than acquiring new customers. Focus on:
- Onboarding: Create a frictionless onboarding process that quickly demonstrates value to new users.
- Customer Education: Develop comprehensive documentation, tutorials, and webinars to help users get the most out of your product.
- Proactive Support: Use tools like Freshdesk (freemium) to provide real-time chat support and proactively reach out to users who may need assistance.
- Feature Adoption Campaigns: Use in-app messaging and email campaigns to drive adoption of key features that improve stickiness.
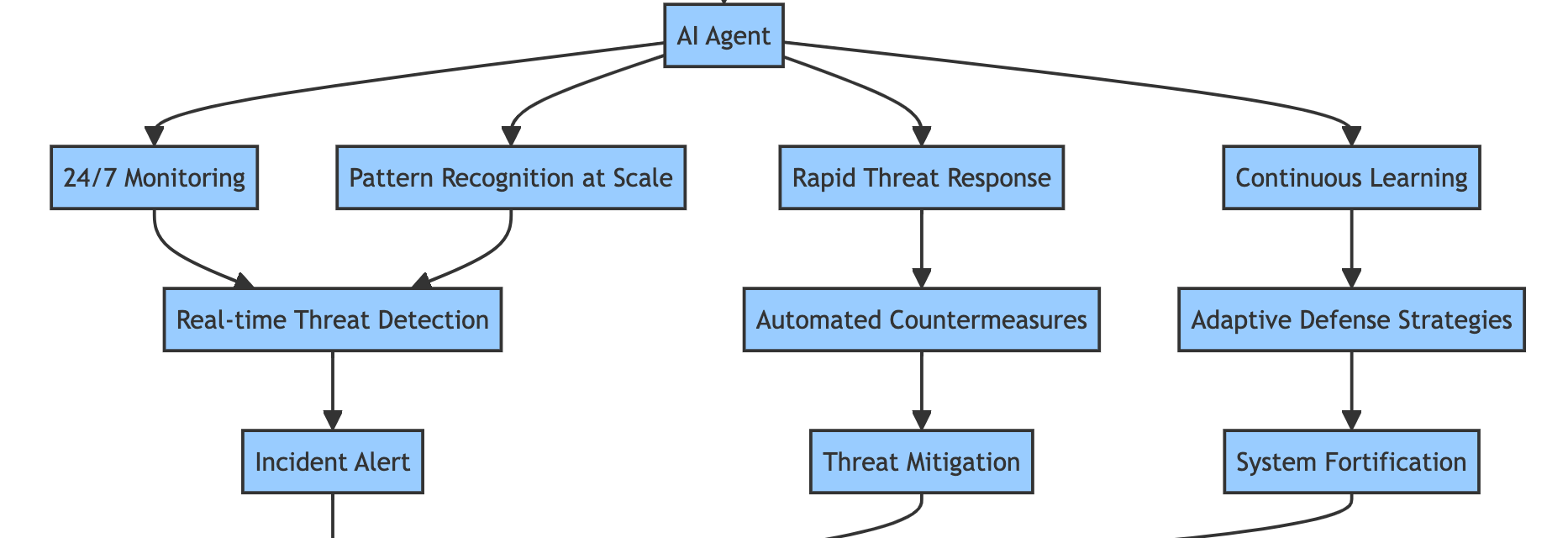
5. Leverage Data and Analytics
Data-driven decision-making is crucial for efficient growth. Use free or low-cost analytics tools to gain insights:
- Google Analytics: Track website traffic and user behavior.
- Mixpanel: Offers a free plan for basic product analytics.
- Amplitude: Provides a generous free tier for event-based analytics.
- Hotjar: Offers limited free heatmaps and session recordings.
Use these tools to identify which strategies are working, where users are dropping off, and what features are driving the most value.
6. Automate and Optimize Processes
Automation can help a small team punch above its weight. Look for opportunities to automate repetitive tasks:
- Zapier: Automate workflows between different apps (free plan available).
- IFTTT: Create simple automated actions (free).
7. Build in Public
"Building in public" involves sharing your startup journey openly, including successes, failures, and learnings. This approach can:
- Generate interest and build an audience
- Attract potential customers and partners
- Provide valuable feedback on your product and direction
Use platforms like Twitter, LinkedIn, or a company blog to share regular updates, metrics, and behind-the-scenes insights.
8. Leverage Your Network
Your professional network can be a powerful asset for bootstrapped growth:
- Reach out to former colleagues or classmates who might benefit from your product.
- Ask for introductions to potential customers or partners.
- Seek mentorship from experienced entrepreneurs in your network.
9. Focus on a Niche
Instead of trying to serve a broad market, focus on a specific niche where you can quickly establish authority and product-market fit. This allows you to:
- Tailor your product more effectively to specific needs
- Build a reputation as a specialist in your niche
- Reduce marketing costs by targeting a more defined audience
10. Prioritize Revenue-Generating Activities
With limited resources, it's crucial to focus on activities that directly contribute to revenue growth:
- Prioritize features that will help close deals with paying customers.
- Focus on marketing activities with a clear ROI.
- Consider offering services (consulting, implementation) alongside your product to generate additional revenue.
Case Study: Bootstrapping Success
To illustrate these principles in action, let's look at the example of Basecamp (37signals). The company bootstrapped its way to success by:
- Starting as a web design firm to generate revenue
- Building tools to solve their own problems, which became their products
- Focusing on a simple, opinionated product that solved a clear pain point
- Leveraging content marketing through their popular blog
- Maintaining a small, efficient team
- Prioritizing profitability over rapid growth
By following these principles, Basecamp grew to over $250 million in annual recurring revenue without ever taking significant outside investment.
Challenging, but Possible
Bootstrapping growth for a B2B SaaS startup is challenging but entirely possible with the right strategies and mindset. By focusing on low-cost, high-impact activities, leveraging available tools and resources, and prioritizing customer value and revenue generation, startups can build a solid foundation for growth without relying on external funding. Remember, the key is to stay lean, be creative, and always focus on providing value to your customers. With persistence and smart execution, bootstrapped startups can compete effectively in the B2B SaaS market and build sustainable, profitable businesses.
https://bit.ly/3AFQI7q
https://bit.ly/4e1T3rN
https://guptadeepak.com/content/images/2024/08/bootstrapping-growth.webp
https://guptadeepak.weebly.com/deepak-gupta/bootstrapping-growth-how-b2b-saas-startups-can-thrive-on-a-shoestring-budget