In the ever-evolving world of cyber threats, protecting a business is akin to fortifying a castle. Just as a castle relies on multiple layers of defense – from its outer walls to its inner keep – businesses must adopt a layered approach to cybersecurity. This holistic strategy is essential in today's digital landscape, where threats are not only external but can also arise from within an organization.
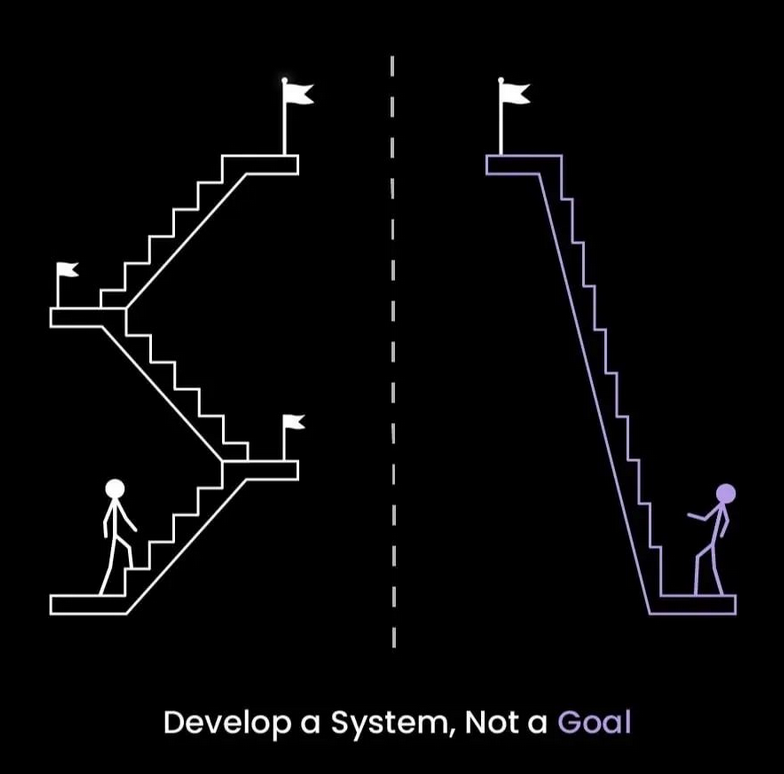
Understanding the Layered Security Model
A layered security model, often referred to as defense in depth, is the practice of implementing multiple security measures at different points in the system. This approach ensures that if one layer is breached, others stand in defense, protecting the core assets of the business.
The Outer Layer: Perimeter Security
The first line of defense is perimeter security, which includes firewalls, intrusion detection systems, and edge network defenses. This layer is akin to the castle walls, designed to repel most external attacks. Regular updates and patches are crucial to keep this barrier robust against emerging threats.
The Middle Layer: Network Security
Once inside the perimeter, network security measures come into play. These include internal firewalls, network segmentation, and intrusion prevention systems. Network security is about controlling who has access to what within the organization, much like a castle's guarded gates that regulate movement between different areas.
The Innermost Layer: Endpoint Security
At the heart of the castle lies the keep, the most heavily guarded area. In cybersecurity, this is endpoint security. It involves securing individual devices (like computers and mobile phones) that connect to the network. Anti-virus software, anti-malware programs, and data encryption are critical components of this layer.
Addressing the Human Element: Training and Awareness
No matter how strong your technological defenses are, the human element can often be the weakest link. Employees need to be trained to recognize phishing attempts, understand the importance of strong passwords, and be aware of the company's security policies.
Regular Training Sessions
Conducting regular training sessions keeps cybersecurity at the forefront of employees' minds. These sessions can range from formal training to sending simulated phishing emails to gauge and improve employee response.
Building a Culture of Security
Creating a culture where security is everyone's responsibility is vital. Encouraging employees to report suspicious activities and rewarding those who adhere to best security practices can foster this culture.
Incident Response Planning
Have an incident response plan for detecting threats quickly and then containing impacts through steps like isolating compromised systems, resetting access controls, and analyzing the root cause.
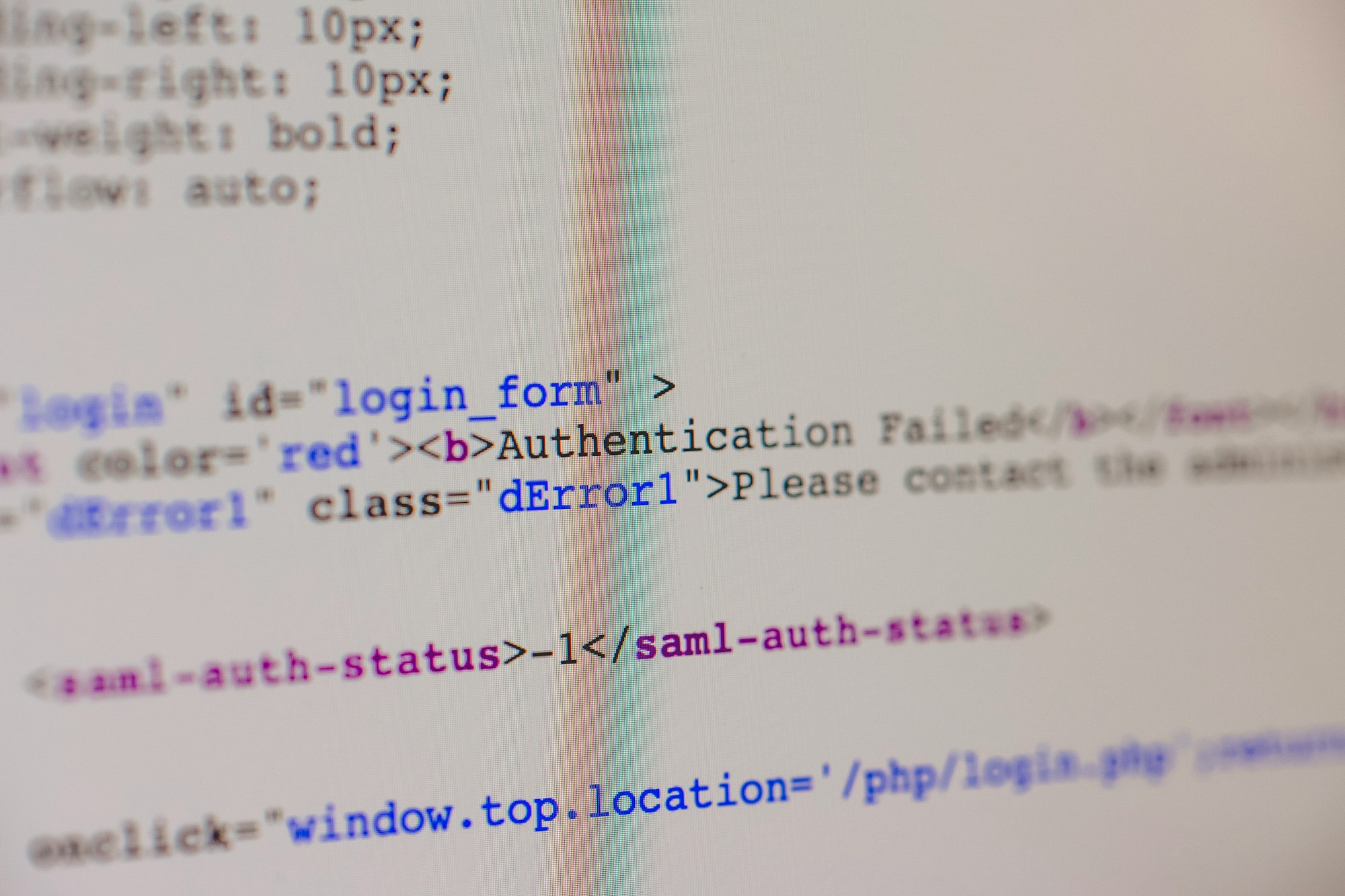
Application Security: Securing the Tools of Trade
Applications are the tools through which businesses operate and interact with the world. Ensuring these tools are secure is paramount.
Secure Development Practices
Incorporating security into the development lifecycle of software – known as secure coding – is essential. This includes regular code reviews, vulnerability testing, and using secure frameworks and libraries.
Regular Application Updates
Applications should be regularly updated to patch any vulnerabilities. This applies not just to in-house software but also to third-party applications used by the business.
Constant Monitoring
Watch activity happening across company networks, systems, email, and cloud apps using security analytics tools. Look for warning signs of compromised accounts, data theft, or policy violations.
Data Security: The Core of the Castle
At the core of every business lies its data – the ultimate treasure that needs safeguarding.
Encryption: Turning Data into Gibberish
Encryption is the process of encoding data so that only authorized individuals can read it. Encrypting sensitive data, both at rest and in transit, ensures that even if data is intercepted or breached, it remains incomprehensible to the attacker.
Access Control: Who Holds the Key?
Implementing stringent access control policies ensures that only those who need to access certain data can do so. This is akin to having different levels of access within a castle, where only select individuals can enter the most sensitive areas.
The Future of Cybersecurity: AI and Machine Learning
As cyber threats become more sophisticated, businesses need to stay ahead of the curve. Artificial intelligence (AI) and machine learning (ML) offer promising avenues.
AI in Threat Detection and Response
AI can analyze vast amounts of data to identify patterns indicative of a cyber attack. This enables quicker detection and response to threats, minimizing potential damage.
Machine Learning for Predictive Security
ML can predict potential vulnerabilities and threats by learning from historical data. This predictive capability allows businesses to fortify their defenses proactively.
Conclusion: An Ongoing Journey
Cybersecurity is not a destination but a journey. As the digital landscape evolves, so must the strategies to protect it. A layered approach to cybersecurity offers a comprehensive defense mechanism, addressing various potential points of failure. However, the key to robust cybersecurity lies not just in technology but in people. Training, awareness, and a culture of security are indispensable in this ongoing battle against cyber threats.
Businesses must be vigilant, adaptive, and proactive in their approach to safeguarding their digital fortresses in this never-ending game of digital chess.
https://bit.ly/42hiMaN
https://bit.ly/3w3KhbK
https://images.unsplash.com/photo-1575475240735-0b191257c762?crop=entropy&cs=tinysrgb&fit=max&fm=jpg&ixid=M3wxMTc3M3wwfDF8c2VhcmNofDR8fG9uaW9ufGVufDB8fHx8MTcwNjQ4ODY3OXww&ixlib=rb-4.0.3&q=80&w=2000
https://guptadeepak.weebly.com/deepak-gupta/protecting-business-from-the-inside-out-a-layered-approach-to-cybersecurity